Mail From (envelope-from <@gator4212.hostgator.com>) ( RFC5321.MailFrom )
Header From From: CEO Name <[email protected]>( RFC5322.From )
Reply-To: CEO Name <[email protected]>
SPF and DKIM only apply on Mail From ( Not header from ) so it passed through DKIM and SPF Protection
Authentication-Results: spf=pass (sender IP is 44.202.169.33)
smtp.mailfrom=gator4212.hostgator.com; dkim=pass (signature was verified)
header.d=hellowonder.co;dmarc=fail action=none
header.from=domain.com;compauth=fail reason=601
DMARC: Set up DMARC to validate the From address domain for senders in Microsoft 365, DMARC uses SPF and DKIM to check for alignment between the domains in the MAIL FROM and From addresses. DMARC also specifies the action that the destination email system should take on messages that fail DMARC, and identifies where to send DMARC results (both pass and fail).
- Look to enable Dmarc in Fail Mode ( Not None )
- We have increased the Anti Phishing Threshold in Defender from 2 to 3
- Make sure all important accounts are added to Impersonation Users in Defender Anti Phish Policy
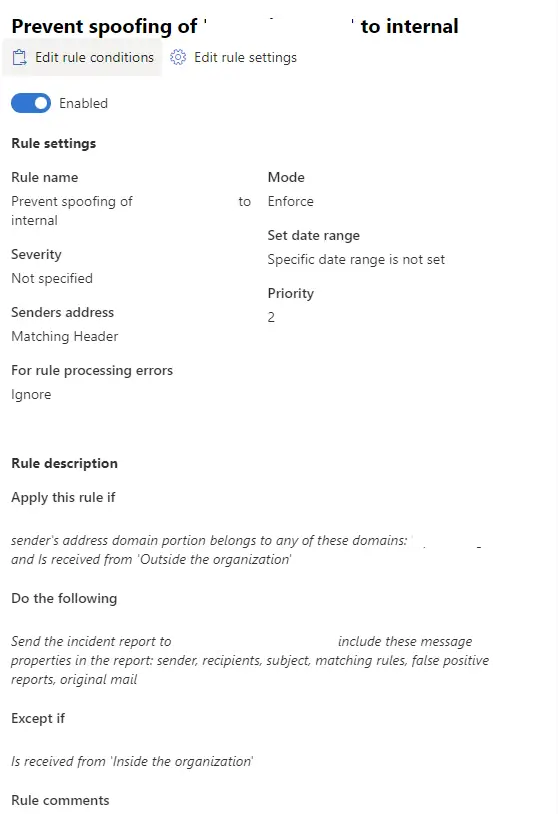
- We have created a Rule in Exchange to Delete any emails with Header From CEO outside the organisation ( Can also try ‘Authentication-Results’ header contains ”compauth=fail reason=601” )

- We have created an Audit Rule in exchange with Header From emails domain.com so we can whitelist any legitimate emails before we turn this rule to delete